Ubiquiti VPN Not Working Here’s How To Fix It Your Guide: Quick Fixes, Tips, And Troubleshooting For Smooth VPN Access
Ubiquiti VPN not working here’s how to fix it your guide. Quick fact: when your VPN drops, it often isn’t the whole network, it’s a misconfiguration, MTU issues, or a certificate hiccup. In this guide, you’ll get a clear, step-by-step path to diagnose and fix common problems, plus practical tips to keep your connection solid. If you’re in a hurry, jump to the quick fixes list below, or keep reading for deeper dives, real-world tests, and shader-sharp troubleshooting.
- Quick fixes at a glance
- Common causes
- Step-by-step troubleshooting
- Advanced tips
- FAQs
Useful URLs and Resources Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence Ubiquiti official docs - help.ui.com NordVPN affiliate link for quick protection - https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
Introduction: Quick Start Guide to Fix Ubiquiti VPN Not Working Ubiquiti VPN not working here’s how to fix it your guide. If you’re scratching your head over why your Ubiquiti VPN isn’t connecting, you’re not alone. Here’s a concise, friendly starter plan:
- Quick fact: most VPN issues come from three areas—network path, authentication, or server configuration.
- First steps 5 minutes: verify internet connectivity, check device time, and ensure firmware is up to date.
- Then test in order: user credentials, certificate validity, port availability, and firewall rules.
- If you’re pressed for time, use the quick fixes below to get back online fast.
In this guide you’ll find: a practical checklist, a troubleshooting table, and a sample config sanity check. Whether you’re at home or managing a distributed network, these tips are designed for real-world use.
Key resources and handy links you’ll want to bookmark:
- Ubiquiti official documentation: help.ui.com
- Community forums for real-world fixes and scripts
- Your device’s admin panel URL and login details
- VPN monitoring tools to watch uptime and latency
What We’ll Cover
- Quick fixes that solve the majority of issues in minutes
- How to confirm when the problem is server-side vs client-side
- Common config mistakes in UniFi USG/Security Gateway and UniFi Dream Machine UDM
- How to verify certificates and TLS settings
- Advanced troubleshooting for flaky connections and intermittent drops
- How to optimize performance using MTU, keepalives, and NAT rules
- A checklist to prevent future VPN outages
Chapter 1: Quick Fixes That Resolve Most Ubiquiti VPN Problems If you’re after fast results, start here. The fixes below apply to UniFi VPN L2TP, IPSec and OpenVPN setups on UniFi devices.
- Confirm Basic Connectivity
- Ensure your internet connection is stable on the device you’re using to reach the VPN.
- Ping your VPN server’s public IP or domain from your client to confirm reachability.
- If you can reach the server but can’t connect, the issue is likely VPN service configuration, not general connectivity.
- Check Firmware Versions
- Update your UniFi Dream Machine UDM, UniFi Security Gateway USG, and any connected access points to the latest official firmware.
- After updates, reboot all devices.
- Verify Time Synchronization
- An incorrect system time can break certificate validation and cause VPN authentication failures.
- Ensure NTP is enabled and the device’s clock is synchronized with reliable time servers.
- Review User Credentials and Access Permissions
- Double-check username, password, and domain if applicable.
- Confirm the user account has the necessary VPN permissions and isn’t locked out due to failed attempts.
- Validate Certificates and TLS Settings
- If you’re using certificate-based authentication, confirm the certificate is valid, not expired, and issued for the correct VPN.
- Check that the certificate chain is complete on both client and server sides.
- Inspect Firewall and NAT Rules
- Ensure VPN ports are allowed through the firewall. Common ports include UDP 500, UDP 4500, and ESP protocol 50 for IPSec; or port 1194 for OpenVPN if used.
- Verify that NAT rules aren’t inadvertently overlapping with VPN traffic.
- Check VPN Server Status and Logs
- Look at the VPN server status in the UniFi Network application.
- Review VPN-related logs for errors such as “authentication failed,” “certificate not found,” or “tunnel negotiation failed.”
- Test with a Different Client Device
- Try connecting from another computer or mobile device to determine if the issue is client-specific.
- If another device connects fine, focus on the original client’s settings.
- Reboot Sequence
- Reboot the client device, the UniFi appliance UDM/USG, and the network path between them.
- Sometimes a simple reboot clears stuck sessions or stale routes.
- MTU and Fragmentation Check
- A mismatched MTU can cause packet fragmentation or dropped VPN packets.
- Start with an MTU of 1200–1400 for IPSec/L2TP setups and adjust in small increments if you experience issues.
Chapter 2: Understanding the Common Causes
- Misconfigured VPN settings: mismatched encryption, phase 1/2 algorithms, or dead peer detection settings.
- Certificate problems: expired certs, wrong common name CN, or incomplete chain.
- Network path issues: ISP blocking, double NAT, or routing loops.
- Client-side issues: outdated app, conflicting security software, or local firewall rules.
- Server-side constraints: license limits, concurrent connections, or high CPU usage on the VPN server.
Chapter 3: Step-By-Step Troubleshooting Guide Follow these steps in order to isolate the problem.
Step 1: Check Internet Access on the Client
- Open a browser, load a few pages, and run a speed test.
- If the internet itself is slow or unstable, fix that first.
Step 2: Confirm VPN Server Reachability
- Use a ping or traceroute to the VPN server’s IP to verify network path integrity.
Step 3: Review User Authentication
- Verify credentials and that the correct authentication method is selected PSK, certificate, or username/password.
Step 4: Validate VPN Configuration
- Compare server and client config for matching parameters: encryption, hash, DH group, and lifetime.
- Ensure the correct pre-shared key PSK or certificate is used.
Step 5: Inspect Certificates
- Check expiration dates and trust chains.
- Confirm the server certificate CN matches the server address you connect to.
Step 6: Examine Firewall Rules and NAT
- Confirm VPN traffic is allowed on required ports.
- Make sure NAT rules don’t translate VPN packets in a way that breaks connectivity.
Step 7: Look at Server Resources
- Check CPU/memory usage on the VPN server; high load can drop connections or slow handshakes.
Step 8: Test with a Clean Client Profile
- Remove existing VPN profiles and recreate them from scratch to rule out profile corruption.
Step 9: Review Logs In Detail
- Look for error codes or messages like “Decrypt error,” “No SA,” or “Negotiation failed.”
- Cross-reference codes with official docs for precise meaning.
Step 10: Perform a Controlled Rollback
- If a recent change caused issues, revert the change to see if the situation improves.
Chapter 4: Advanced Tips for Stability and Performance
- Optimize MTU: Start with 1400 and adjust downward if you see fragmentation indicators in log files.
- Use Dead Peer Detection intelligently: Enable DPD on both sides with reasonable timeouts to recover quickly from dead tunnels.
- Split tunneling vs full tunneling: Decide which traffic should go through the VPN for speed vs security.
- DNS considerations: Point VPN clients to a private DNS server to prevent leaks and improve resolution speed.
- Regular health checks: Schedule automatic reboots during low-usage windows to refresh tunnels.
- Monitoring and alerting: Set up uptime bots and alert thresholds so you’re notified of drops or latency spikes.
- Redundancy planning: If you rely on VPN for critical operations, add a secondary VPN path or a failover strategy.
Chapter 5: Real-World Scenarios and Solutions
Scenario A: VPN connects but drops after a few minutes
- Likely cause: NAT or MTU issues, or server side resource limitations.
- Solution: verify MTU, monitor server load, and check keepalive settings.
Scenario B: Authentication failures after password change
- Likely cause: cached credentials, or policy requiring MFA.
- Solution: clear saved credentials, re-enter new password, ensure MFA tokens are synchronized.
Scenario C: Client reports “certificate not trusted”
- Likely cause: missing CA on client, expired server cert, or wrong CN.
- Solution: install the correct CA, renew certs, verify CN matches.
Table: Quick Reference Troubleshooting Checklist
- Internet connectivity: OK / Not OK
- Server reachability: Ping/Traceroute successful? Yes/No
- VPN credentials: Correct? Yes/No
- Certificate status: Valid? Yes/No
- Firewall ports: Open? Yes/No
- MTU: Optimal? Yes/No
- Server load: Under capacity? Yes/No
- Client device: Fresh profile? Yes/No
Section: Practical Setup Tips And Example Configurations
- Example 1: IPSec VPN on UDM Pro with PSK
- Phase 1: IKEv2, AES-256, SHA-256, DH Group 14
- Phase 2: ESP AES-256, AES-GCM, PFS group 2
- PSK: your-strong-key-here
- NAT-T enabled, Dead Peer Detection enabled, MTU 1400
- Example 2: OpenVPN on UniFi OS
- Ensure server.conf matches client.ovpn details
- Use TLS authentication to reduce brute-force chance
- Enable TLS 1.2 or higher
Section: Security Considerations
- Use strong, unique credentials and rotate them periodically.
- Prefer certificate-based authentication over PSK where possible.
- Keep VPN servers behind an additional layer of protection, like a firewall or IP allowlist.
- Monitor for unusual login attempts and apply MFA if supported.
Section: Maintenance And Prevention
- Schedule quarterly firmware updates and configuration reviews.
- Maintain a small change log to track modifications to VPN settings.
- Regularly verify certificates and revoke if compromised or expired.
- Test VPN recovery after network changes or ISP updates.
FAQ Section
Frequently Asked Questions
How do I know if the VPN server is down?
If clients can’t connect but the VPN service status shows as running, check logs for “server not responding,” verify CPU/memory usage, and confirm the service isn’t blocked by a firewall or policy.
Why does my VPN keep disconnecting?
Intermittent disconnects are often MTU-related, NAT traversal issues, or high server load. Check MTU, ensure keepalives, and monitor server health.
Can I use VPN with a dynamic IP?
Yes, but you’ll likely need a dynamic DNS entry or a static external address. Ensure the client uses the domain name consistently.
Is OpenVPN supported on UniFi devices?
Yes, UniFi supports OpenVPN through various configurations, but the setup may differ from IPSec/L2TP. Follow the official docs for OpenVPN specifics.
Should I enable Dead Peer Detection?
DPD helps recover from broken tunnels faster. Enable it on both client and server sides with reasonable timeouts. Forticlient vpn 다운로드 설치부터 설정까지 완벽 가이드 2026년 최신 — Forticlient VPN 설치 방법, 설정 팁 및 보안 이슈까지
How can I speed up VPN connections?
Optimize MTU, minimize encryption overhead by selecting efficient ciphers, reduce unnecessary routing, and consider split tunneling for non-critical traffic.
What ports should I open for IPSec on UniFi?
Typically UDP 500, UDP 4500, and ESP protocol 50. If using NAT-T, UDP 4500 is critical.
What certificates are required for VPN authentication?
You’ll need a server certificate, a CA certificate to trust the server, and a client certificate for certificate-based auth or a PSK for pre-shared key setups.
How do I test VPN configurations safely?
Use a test client on a non-production device, connect to a test network, and monitor logs. Change one setting at a time to see its effect.
Where can I find more detailed official guidance?
Visit help.ui.com for official UniFi VPN configuration docs, and check community forums for real-world troubleshooting threads. The Best Free VPN for China in 2026 My Honest Take What Actually Works
End of Guide
Sources:
Does nordvpn have a free trial for iphone heres the real deal
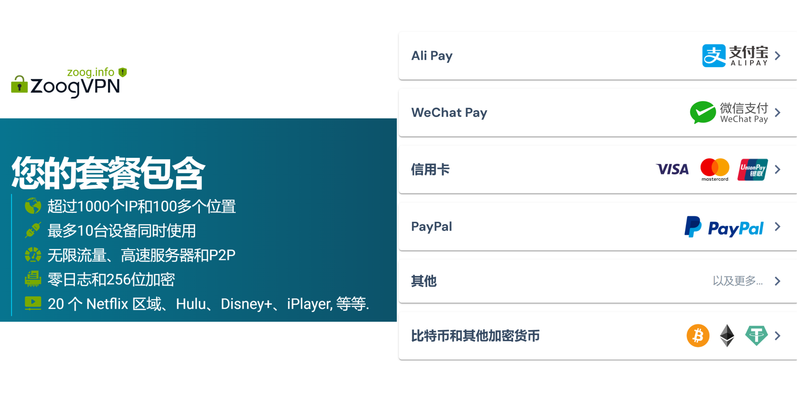
2026年最佳免费翻墙VPN推薦:安全穩定上網指南
Nordvpn 使用教學:2026年完整指南 註冊、設定、使用秘笈與技巧
2025年最佳机场vpn推荐:速度、稳定与安全的终极指南、机场WiFi下的快速连接、跨境访问与隐私保护完整攻略 미꾸라지 vpn 다운로드 2026년 완벽 가이드 설치부터 활용까지: VPN 최적 활용과 보안 팁, 빠른 설정 비법
Unifi edgerouter-x vpn 2026